
Finally got hacked after 6 years of safe journey online.
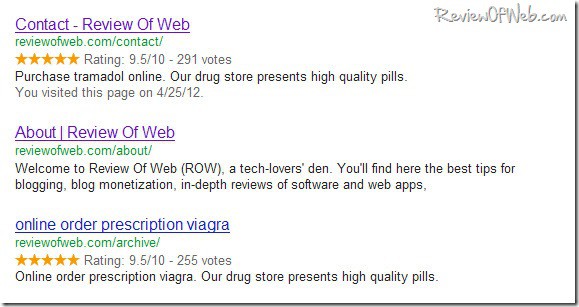
Two weeks back, a simple site search site:ReviewOfWeb.com on Google revealed some unwanted results which clearly showed that my site was under attack. Here is how some of my site URLs looked like in Google. [Check the description.]
The interesting thing about this hack was that it was a conditional redirect, or in simple words, when you would navigate to this site by directly entering the URL in address bar, you would get the actual page of my website but when a visitor arrives from a search engine he would get re-directed to the spammers website in what was probably an iframe.

What should you do in a similar situation?
Calm down! It is unnerving to see your site being surrounded by malware and Google showing nasty links and text below your site URL, but the damage is done and you have to correct that. Worrying about it may make the matter worse.
How to identify the files that got hacked?
SSH to login to your website and find the last modified files by the timestamp. You can ask your webhost. In my case the hacker had inserted a base64_decode() in my wordpress header file. Though I was able to nail down the files which were hacked, just to be doubly sure I preferred to hire a professional malware removal agency Sucuri.net
Folks at Sucuri were super fast and removed the malware within half and hour of opening a ticket with them. They followed up with some general recommendations on how to prevent further attacks. The recommendations included changing FTP credentials, wordpress login credentials, database passwords, updating core wordpress, wordpress plugins and running a thorough virus scan on the personal machine. I did as advised by them.
To my surprise, within 2 hours the malware returned, this time affecting another file – index.php
This was more worrying since it seemed the intruder was targeting at will. While it is relatively easy to identify the files that get hacked, at times it is extremely difficult to identify how the intruder reached those files. Since I had already updated my wordpress installations and changed passwords, I nailed down three possibilities –
- A vulnerable wordpress plugin that is not updated by the developer.
- Vulnerable wordpress theme.
- Open permissions (chmod 777) on my shared server.
First, I uninstalled all the plugins, removed all except the core tables from the wordpress database and then did a fresh reinstall of the plugins that were really required. Along with that, I also changed my theme framework from Woo Theme to the current Thesis theme (In the recent past, WooTheme framework had been targeted twice). There was an unused script in my account whose temp folder had open permissions, which I fixed.
Final Cleanup act
The excellent folks at Sucuri – a special thanks to David Dede – did the clean up once again and since then this site is pretty safe. Sucuri not only provides clean up services but they also provide a facility whereby your site is checked every 6 hrs for any major/core file changes. A premium wordpress plugin is included which helps in 1 click ‘hardening’ of wordpress installation, logging changes to your wordpress files and blocking bad bots from visiting your website. I have now upgraded my plan at Sucuri and secured all my sites. You can check more about Sucuri here
Over to you. Have you ever got hacked? How did you clean the mess? More importantly were you able to identify the source?
 Ankur Jain is a Software Engineer in Test Automation. After a 5 years stint with Accenture and Oracle, he started his eLearning company. A long-time blogger and proud owner of the "Learn" series of websites.
Ankur Jain is a Software Engineer in Test Automation. After a 5 years stint with Accenture and Oracle, he started his eLearning company. A long-time blogger and proud owner of the "Learn" series of websites. 
meri ek website h vo hack ho gayi or aab admin ma khul nhi rhi kyu kru plz tell me
@yashwant: I understand it’s a scary situation. Try to be calm and ask the folks at Sucuri for help. They are excellent at what they do.
Yepperoonie.
Glad you got yours sorted. It’s a bugger that one.